App security is a lot of things, but sometimes we need to stop and consider what it isn’t, particularly as the volume and frequency of applications developed and deployed to meet the insatiable demand continues to rise.
1. Not a high priority – but it should be
A staggering 44% of respondents to a survey sponsored by Arxan and IBM on the security of IoT and mobile applications admitted they aren’t doing anything to prevent an attack. Lest you dismiss said responses as being related to a small subset of your application portfolio, let’s consider WhiteHat Security’s seminal annual report on web security statistics, which found “about one third of Insurance applications, about 40% of Banking & Financial Services applications, about half of Healthcare and Retail applications, and more than half of Manufacturing, Food & Beverage, and IT applications are always vulnerable.”
“Always vulnerable” in the WhiteHat Security vernacular is defined as “vulnerable on every single day of the year.”
What’s more, the same report found “the average time-to-fix varies by industry from approximately 100 days to 245 days.” For retail and healthcare, it’s about 200 days. Technology and IT lag further behind at an average of 250 days time-to-fix a vulnerability.
It’s that first laissez-faire approach to security that makes the latter so difficult to swallow. If app security isn’t high on the priority list, it’s a sure bet that a significant percentage of applications (or APIs serving data to applications) are vulnerable.
2. Not just about the app
There’s a misconception that app security is only about the application. If an app were a stand-alone entity, perhaps that would be true. But apps are deployed on platforms, rely on third-party scripts and APIs, and integrate with systems responsible for managing data. That means app security is a stack that requires careful attention to all components, not just the app itself. The OWASP Top Ten is a good place to start for apps, but let’s not ignore that protocol-level (TCP, HTTP, and TLS) vulnerabilities in platforms have been a significant source of heartburn in the past decade.
And let’s not ignore the relationship between volumetric network attacks and more insidious system and app-layer attacks. Dark Reading noted this correlation in a recent article:
“Nearly half of the impacted organizations say their DDoS attacks coincided with some form of breach or malicious activity on their networks, including data theft and ransomware. For instance, 47% report discovering virus activity on their network after a DDoS attack, 43% cite malware as being activated, and 32% report customer data theft.”
App security requires attention to the entire app architecture, which includes the network, data, and services that scale and secure that app.
3. Not somebody else’s problem
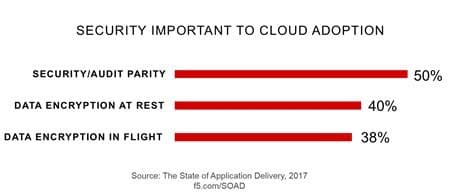
With 1 in 5 organizations planning to host over 50% of their applications in the cloud according to our 2017 State of Application Delivery survey, securing apps becomes more challenging. Shipping an app off to “the cloud” may redistribute responsibility for a portion of the security burden, notably that of the network and system-level components. But the app and its platforms and the external scripts and resources the app relies on are still your responsibility. Ensuring the same level of security in the cloud as is present on-premises can be challenging, particularly when mixing and matching native cloud services that aren’t compatible at the policy-level with those on-premises.
But it’s a challenge that needs to be met, either by ensuring consistency of the services enforcing those policies across on-premises and in the cloud, or by shifting app security duties to a service-based offering that can offer consistency for both at the same time, or by carefully hand-crafting equivalent policies for cloud-native services.
Whatever route you choose, the responsibility remains yours.
The impact of breaches in terms of brand reputation, consumer trust, and the potential for future exploitation (in the case of stolen credentials) makes app security more important than ever. Leaving it to the last minute or assuming someone else will take care of it is a recipe for disaster. Recognizing its importance and placing a higher priority on testing and remediation while taking advantage of the architectural options afforded by cloud and cloud-supporting services will go a long way toward reducing your risk.
App security is not optional.
About the Author

Lori MacVittie is a Distinguished Engineer and Chief Evangelist in F5’s Office of the CTO with deep expertise in application delivery, automation strategy, and infrastructure. She is known for turning complexity into clarity whether she’s defining guardrails for AI agents, dissecting brittle multicloud architectures, or probing the limits of scalable systems. She brings more than thirty years of industry experience across application development, IT architecture, and network and systems operations. Before joining F5, she served as an award-winning technology editor. MacVittie holds an M.S. in Computer Science and is a prolific author whose publications span security, cloud, and enterprise architecture. She is also an avid tabletop and video gamer with unapologetically strong opinions about cheese.
More blogs by Lori Mac VittieRelated Blog Posts

Secure-by-design storage for agentic AI: Why runtime visibility plus traffic control matters
Learn how F5 is collaborating with NVIDIA to help protect agentic AI with secure-by-design AI infrastructure, runtime visibility, and traffic control.

F5 joins the Dell AI Ecosystem Program to help enterprises operationalize AI
F5 joins the Dell AI Ecosystem Program to help enterprises deploy production AI with greater performance, security, and control.

Why sub-optimal application delivery architecture costs more than you think
Discover the hidden performance, security, and operational costs of sub‑optimal application delivery—and how modern architectures address them.

Architecting for AI: Secure, scalable, multicloud
Operationalize AI-era multicloud with F5 and Equinix. Explore scalable solutions for secure data flows, uniform policies, and governance across dynamic cloud environments.

AppViewX + F5: Automating and orchestrating app delivery
As an F5 ADSP Select partner, AppViewX works with F5 to deliver a centralized orchestration solution to manage app services across distributed environments.
F5 NGINX Gateway Fabric is a certified solution for Red Hat OpenShift
F5 collaborates with Red Hat to deliver a solution that combines the high-performance app delivery of F5 NGINX with Red Hat OpenShift’s enterprise Kubernetes capabilities.
