F5 first introduced F5 BIG-IP Access Policy Manager (APM), our access control management solution in 2008. In its 18 years, BIG-IP APM has amassed not just a great customer base, but a passionate user following. Having personally been to over 10 RSA Conferences with F5 and having served as a product marketing manager responsible for BIG-IP APM, I can honestly tell you that I have never, ever met any customer who wasn’t enamored with BIG-IP APM.
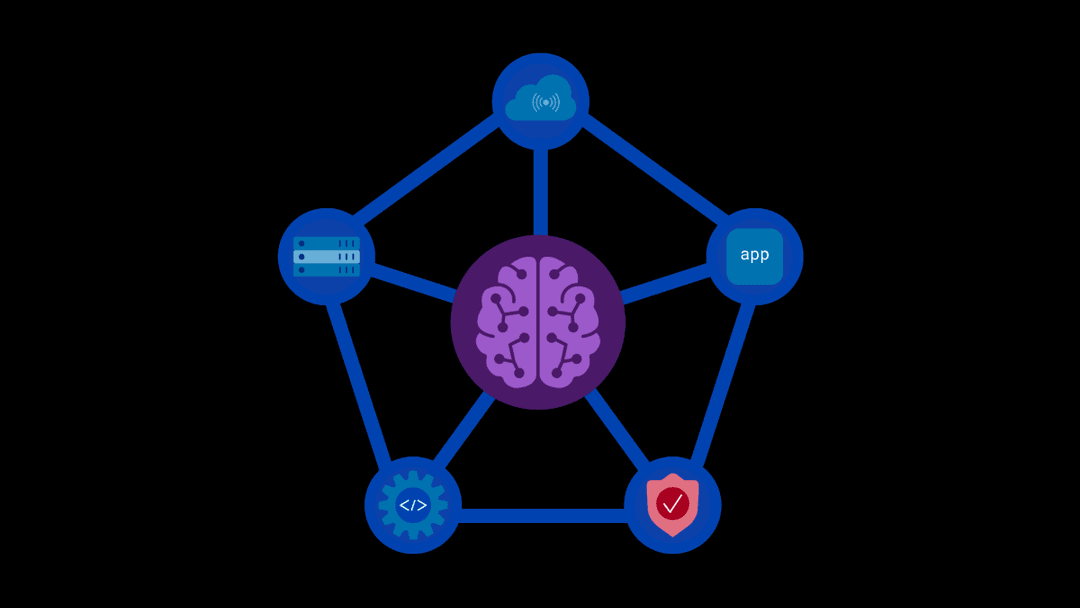
A market-leading secure remote access solution, BIG-IP APM’s capabilities and innovation have continued to increase over its many years as a renowned F5 product. The use cases that BIG-IP APM addresses are myriad:
- Secure remote access (SSL VPN)
- Identity federation
- Virtual application access management
- Remote application access
- Enterprise mobility management, and
- API authorization, authentication, and protection.
One of the more recent capabilities added to the ever-growing number of use cases successfully addressed by BIG-IP APM has been zero trust application access, through its support of Identity Aware Proxy (IAP).
“Given the importance of zero trust in today’s market, F5 has decided to take a major step forward and rename F5 BIG-IP Access Policy Manager (APM), F5 BIG-IP Zero Trust Access”
What is Identity Aware Proxy (IAP)?
Identity Aware Proxy enables secure, context-aware access to applications and services based on a user’s identity and the context of their request. Introduced by Google in 2017 as part of its BeyondCorp Enterprise initiative, and now primarily associated with Google Cloud, IAP is a zero trust operational model. What that means is that it follows the mantra of zero trust espoused by the U.S. National Institute of Standards and Technology (NIST) of “never trust, always verify.”
IAP not only verifies user identity before allowing access to an application— the who of access, represented by authentication and authorization (two of the three AAAs of computer security), but it also verifies the context of the user’s application access request—the what, where, why, and how of access.
Zero trust application access
But BIG-IP APM takes these checks further by limiting a user who meets the policies applied for user identity and the context of their application access to accessing a single application. It’s a one-to-one relationship between the user and the application to which they’ve been granted access based on passing identity- and context-aware policies in BIG-IP APM.
The approved user can only access a single application at a time. (Now that’s least privilege access.) Their identity can be federated to additional apps after passing the identity check when accessing their first application. However, if they decide they want to access another application, then the entire policy check for user identity and application access context starts over, including a recheck of the user’s identity. Once a user is approved to access their second application, their access granted to the first application is terminated. They can only access one application at a time. It’s called “per request application access,” and it’s a zero trust operational model.
This means that BIG-IP APM delivers zero trust application access. It limits horizontal movement between applications by keeping user application access bounded to a single application at a time, providing least privilege.
BIG-IP APM becomes BIG-IP Zero Trust Access
With this in mind and given the importance of zero trust in today’s market, F5 has decided to take a major step forward and rename BIG-IP Access Policy Manager (APM), BIG-IP Zero Trust Access.
But wait, you may ask: What happens to all the other great use cases that BIG-IP APM addresses? Is F5 going to stop support for those use cases?
The answer is an emphatic “NO.” With the name change to BIG-IP Zero Trust Access, F5 will continue to support the existing BIG-IP APM use cases. We completely understand the power that BIG-IP APM delivers and how much our customers depend on the array of use cases it supports. We will continue to support the existing BIG-IP APM use cases for as long as they are important and viable in the market and to our customers.
The future is now (or at least soon)
In addition, over the coming months, you can expect to see many exciting new features and innovations that address even more use cases with BIG-IP Zero Trust Access. In our next release, slated for later this year, we will be introducing:
- IPSec VPN for customers who require additional security for their secure VPN access.
- Dynamic Client Registration (DCR), which enables clients to dynamically register with an authorization server or identity provider (IdP) without requiring pre-configuration. This is a key enabler for zero trust security, scalable identity management, and cloud-native automation, and is particularly useful today for AI agents, MCP servers, and IoT devices.
- Post-quantum cryptography (PQC) for SSL VPN clients, delivering quantum-resilience and enabling crypto-agility for our remote access customers today and into the future.
So, as you can see, BIG-IP Access Policy Manager (APM) isn’t going away; it’s just changing its name. Long live BIG-IP APM!
You will start to see the name change from BIG-IP Access Policy Manager (APM) to BIG-IP Zero Trust Access on the F5.com website and in materials beginning this week.
Thank you for your continued support of and dedication to BIG-IP APM, now BIG-IP Zero Trust Access.
To learn more, please visit the newly named BIG-IP Zero Trust Access web page.
About the Author

Related Blog Posts
F5 Distributed Cloud Services: Security innovation built for operational scale
Learn how the latest upgrade to F5 Distributed Cloud Services advances AI driven security while strengthening the operational foundations teams need to run at scale.
From dashboard fatigue to operational excellence: Why XOps needs F5 Insight for ADSP
Learn how F5 Insight for ADSP lays the visibility foundation for XOps—turning fragmented signals across applications and infrastructure into actionable intelligence.
The hidden cost of unmanaged AI infrastructure
AI platforms don’t lose value because of models. They lose value because of instability. See how intelligent traffic management improves token throughput while protecting expensive GPU infrastructure.
Govern your AI present and anticipate your AI future
Learn from our field CISO, Chuck Herrin, how to prepare for the new challenge of securing AI models and agents.

F5 recognized as one of the Emerging Visionaries in the Emerging Market Quadrant of the 2025 Gartner® Innovation Guide for Generative AI Engineering
We’re excited to share that F5 has been recognized in 2025 Gartner Emerging Market Quadrant(eMQ) for Generative AI Engineering.
Self-Hosting vs. Models-as-a-Service: The Runtime Security Tradeoff
As GenAI systems continue to move from experimental pilots to enterprise-wide deployments, one architectural choice carries significant weight: how will your organization deploy runtime-based capabilities?
