Shift (Web App) Security Lefter
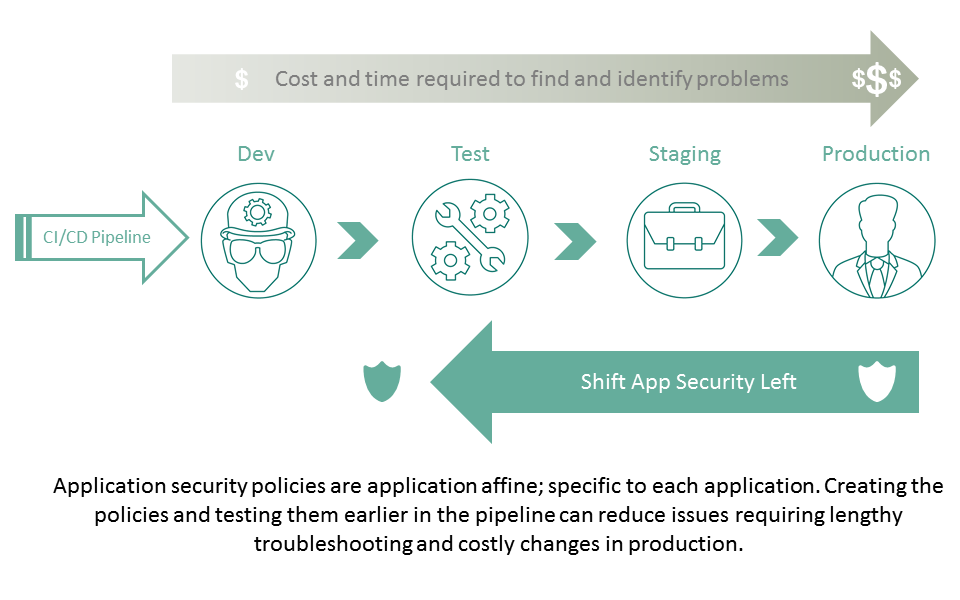
The concept of "shifting left" for appropriate IT concerns is growing. The notion is basically to shift more into the app dev delivery pipeline functions that, when applied earlier, can result in greater stability and security of the resulting code. Security is one of those functions that can yield significant benefits in terms of reducing the conflicts and errors that crop up in production and cost time and money the business would rather not spend.
Most of the time the security functions proposed as being ready to "shift left" are those that relate directly to code: vulnerability scanning, automated patching, intrusion detection and similar services. What is rarely (in fact probably never until this post) mentioned is the benefits of shifting web application firewall functions left.
There is good logic behind shifting this kind of functionality left, namely application affinity. Highly application affine services like web application security and load balancing and optimization are specific to an application. Not a protocol like HTTP, but to the actual application itself. Application security and optimization, in particular, often contain configurations that require understanding specific URIs (like RESTful API calls), the types of data being exchanged (and its formats), as well as identifying users and devices that may be specific to the app or specific portions of the app.
That means a web application security policy is based pretty much on the application, which means that policy is good for that application alone. Matching data and URIs can (and does) introduce the potential for errors which means an application that breaks. When that error first shows up in production, heads roll. Time is spent, money is wasted and the caffeine budget for the week skyrockets and leaves everyone else drinking colored water for the rest of the month. Not good at all.
Shifting the configuration and testing of these application affine policies lefter, into test, can be a significant boon in terms of eliminating most (hopefully all but, Heisenberg) conflicts or errors and ensuring a smoother, faster and less complicated roll out through the production pipeline.
The increasing availability of software and virtual editions of traditional web application firewall services means the ability to provision these services in a broader number of environments and ensure higher levels of access lefter in the deployment pipeline. Shifting web application security lefter also means the ability to apply vulnerability scanning to the web application security service while it's protecting the application under test, giving security ops and dev a better understanding of the interaction between the two as well as the opportunity to tweak policies to ensure proper (expected and desired) behavior. Policies, especially those that might be encapsulated in template form, are easy enough to move between environments and can be treated as code - stored in repositories and versioned for future use.
The availability of APIs and templates along with virtualization of traditionally network-hosted application affine services makes it possible for organizations to shift security lefter and achieve real gains in optimizing the production pipeline process.
